-

Creating Custom Solidity Libraries For Reusable Code
Solidity libraries enable blockchain developers to create modular reusable code. This shared usage avoids duplicating code, saves gas during deployment and promotes consistency within a code base. Let’s create a basic library that demonstrates how this works: This code defines a simple smart contract that utilises a library for basic arithmetic operations. The MyMath library
-

Building Smart Contract Event Filtering Systems for DApps
How events work in web3 Events in Web3 act as logs of significant occurrences within a smart contract. When a specific function is executed, the smart contract can “emit” an event, signalling to external systems that something has happened. These emitted events are stored on the blockchain, but they do not modify the contract’s state.
-

Automating Web3 Interactions In Rust | Minting Ethereum NFT’s With Ethers-rs
In this tutorial we are going to be deploying a simple NFT contract to Ethereum and then minting new NFT’s using a bot built with Rust and ethers-rs Let’s start by heading to Remix and deploying this contract to Ethereum’s Sepolia testnet. It has already been deployed here if you want to skip this step:
-

Building A Cross Chain Token Bridge With LayerZero v2
This tutorial will guide you through the process of building a token bridge using LayerZero v2, specifically employing the OFTAdapter on mainnet and the OFT.sol contract on all other chains. We’ll cover the setup and deployment workflow, ensuring you have a comprehensive understanding of the process. Before we delve into the deployment process, it’s crucial
-

Practical Applications Of Merkle Trees
Merkle trees are a useful tool for blockchain developers offering a myriad of benefits, chief among them being the efficient verification of large data sets and proof of inclusion. By leveraging Merkle trees developers can significantly optimise gas costs and enhance the overall performance of their decentralised applications. In this article we will look at
-

How To Connect An Arduino To A Soroban Smart Contract
This tutorial will guide you through the process of connecting an Arduino to a Soroban smart contract on the Stellar blockchain. We’ll create a system where blockchain events can trigger physical actions through an Arduino. James On YouTube Watch On YouTube: https://youtu.be/C4a9O7AFAVc | Subscribe All the code for this project is open source at: https://github.com/jamesbachini/Arduino-Soroban-Controller
-

Implementing RBAC Patterns in Solidity
We can implement role based access control or RBAC patterns in Solidity using OpenZeppelin’s AccessControl.sol library. This allows developers to manage different roles and assign permissions dynamically. Here’s a step by step guide based on the information provided. Understanding Roles in Access Control The essence of RBAC in Solidity involves defining roles, where each role
-

The Future Of Prompt Engineering | Best Practices For LLM Models
This article will explore how prompt engineering for LLM models like ChatGPT is evolving and how you can stay ahead of the game. Prompt Design Principles As large language models (LLMs) continue to evolve, the art of prompt engineering has become increasingly crucial. At its core, effective prompt design hinges on clarity, specificity, and context
-

Tokenomics 101 Designing Effective Token Models
Tokenomics Fundamentals Tokenomics refers to the economic model and framework that governs the use, distribution, and value of tokens. At its core, tokenomics is the study of the supply and demand of tokens, how they incentivise users and developers, and the role they play in driving network effects. Unlike traditional currencies, tokens are highly versatile
-

Why Inflows Into Spot Bitcoin ETFs Don’t Push Prices Up
The Bitcoin Spot ETFs are a gateway for institutional inflows into Bitcoin, potentially driving up prices. However, on the 29th and 30th October over $1.763 Billion USD flowed into the Bitcoin ETFs*. During this period the BTC/USD price barely moved. Here’s a closer look at why spot Bitcoin ETF inflows don’t always translate into an
-

Marketing Psychology in Web3
This article delves into the key aspects of marketing psychology that are unique or particularly relevant to the Web3 ecosystem, exploring how trust, community engagement, scarcity, fear of missing out, attention economy, and behavioural economics intersect with this innovative space. Trust and Credibility The blockchain sector has been plagued by numerous fraud & scams, making
-

Meridian 2024 Takeaways
Key Innovations and Infrastructure Developments from Meridian 2024 The recent Stellar Meridian conference and its preceding hackathon showcased significant developments in the Stellar Network’s ecosystem, highlighting how the platform is revolutionizing blockchain infrastructure and smart contract capabilities. From innovative on/off-ramp solutions to ground breaking smart wallets, Stellar is positioning itself as a formidable player in
-

Creating MultiSig Wallets with Solidity
MultiSig wallets have become increasingly popular due to their enhanced security features. In this article, we will delve into the key components of a MultiSig wallet, how to write a MultiSig wallet contract using Solidity, deploying the wallet, and handling deposits and withdrawals. Note that the code provided here is for educational purposes only. If
-

Simple Example Of Rust Struct & Importing Modules
One powerful feature in Rust is how it organizes code into modules and allows the reuse of code with structs and methods. In this tutorial, we’ll walk through a simple example to illustrate how to define and use a struct in Rust and how to import modules for organization. Step 1: Define the Module and
-

Prediction Markets Solidity
Prediction markets are decentralized platforms where participants can bet on the outcome of future events. For example, people could bet on the outcome of a presidential election or a sports game. In this tutorial, we will walk through a smart contract built on Ethereum, which allows users to create and participate in prediction markets. The
-

Incorporating Bitcoin In A Treasury Strategy
Cash Savings in Treasuries Treasury managers face a significant challenge in preserving the value of their reserves. Traditional cash savings, once considered a safe haven, have become increasingly unsuitable for long-term corporate savings. This shift is primarily due to the ongoing dilution caused by money supply growth, as central banks worldwide engage in quantitative easing
-

A Simple Browser Resource Monitor
This single index.html file can be uploaded to any web server, run locally, or accessed here: https://jamesbachini.com/misc/browser-resources.html It enables web developers to monitor browser resources over time and test different devices processing abilities. The dashboard first collects and presents fundamental system information, providing context about the environment in which the application operates. This data includes:
-

Stellar Soroban Boilerplate
In this tutorial I’m going to go through the code for a boilerplate which connects a Soroban smart contract to a React dApp. Note that for a more full featured demo app you can check out the excellent Scaffold Soroban at: https://developers.stellar.org/docs/learn/interactive/dapps/scaffold-soroban There is also this from the guys at Palta Labs:https://create-soroban-dapp.paltalabs.io/ James On YouTube
-

AI Predictions | How Close Are We To AGI?
In recent years, the field of artificial intelligence has witnessed remarkable advancements, particularly in the domain of large language models. These sophisticated systems like ChatGPT have demonstrated impressive capabilities in natural language processing, coding, and problem solving. However, the question remains “how close are we to achieving true artificial general intelligence?” James On YouTube Watch
-

Decentralized Lending Pools | Blend Capital
Overcollateralized lending has emerged as a cornerstone in the decentralised finance ecosystem, providing a secure and efficient way for users to borrow and lend digital assets. Blend Capital leverages this mechanism on Stellar’s Soroban smart contract platform, introducing a robust protocol for overcollateralized lending and borrowing. This article delves into how overcollateralized lending works, explores
-

Encrypting Private Keys in .env
It has become very normalised to store Ethereum private keys in plain text within .env files. While this is convenient, it’s a disaster waiting to happen when working in production with wallets that contain real funds. Today, I’ll show you a better way to manage your hot wallet keys using AES encryption. Full code for
-

Balancer v3 Hooks
For the Balancer v3 Hookathon (yep it’s a hackathon to create DeX hooks) I had the idea to try and create a fair launch memecoin platform. It’s the kind of thing that could bring utility to the ecosystem as we’ve seen recently with the wave of memecoin trading on Solana. The target is to create
-

Creating WASM Files Using Rust and Running Them in the Browser
In this tutorial we will be writing some code in Rust, compiling to web assembly (WASM) and then running that code in a browser. This enables high performance applications to be run within a web dev setting. In this tutorial I’ll be using windows subsystem for Linux. Let’s first install Rust and wasm-pack (more instructions
-

Understanding ABI Encoding: A Guide to abi.encodeCall and encodeWithSelector
What Is ABI Encoding Application Binary Interface (ABI) encoding is a crucial concept in Ethereum smart contract development. It serves as a standardised method for encoding function calls and data, enabling seamless communication between different components of the Ethereum ecosystem. ABI encoding ensures that data is consistently formatted and interpreted across various platforms and programming
-

How to Host Your Own Generative AI Model with Flux
Why Host Your Own Flux Model Hosting your own AI model offers significant benefits, particularly for users who demand fine control over image generation, privacy, and customisation. Unlike public cloud-based APIs, which may impose usage limitations or fees, self-hosting gives you full control over how the model operates. You can adjust hardware configurations, implement optimised
-

Enums In Solidity
Enums are one of the most useful and underused data types in Solidity. I think because they aren’t widely used in Javascript and web dev, they often get overlooked in contract development. In this article I’ll make my case for why enums deserve a place in your tool kit and smart contracts. Enums in Solidity
-

WebAuthn PassKey Smart Wallets
In this article we will take a glimpse into the future of account abstraction where web3 can offer walletless, passwordless authentication to web applications. I’ll be connecting a Stellar Soroban smart contract to a web3 frontend and verifying signatures from biometrics on your phone. Welcome to the future. The full source code used in this
-

React Hooks Tutorial | The 7 Most Important React Hooks
React Hooks provide a way to manage state, side effects, references and more in functional components. In this tutorial, we’ll look at the seven most commonly used React hooks When You Would Use These React Hooks useStateImagine you have a piece of data in your component that might change, like a number for a counter
-

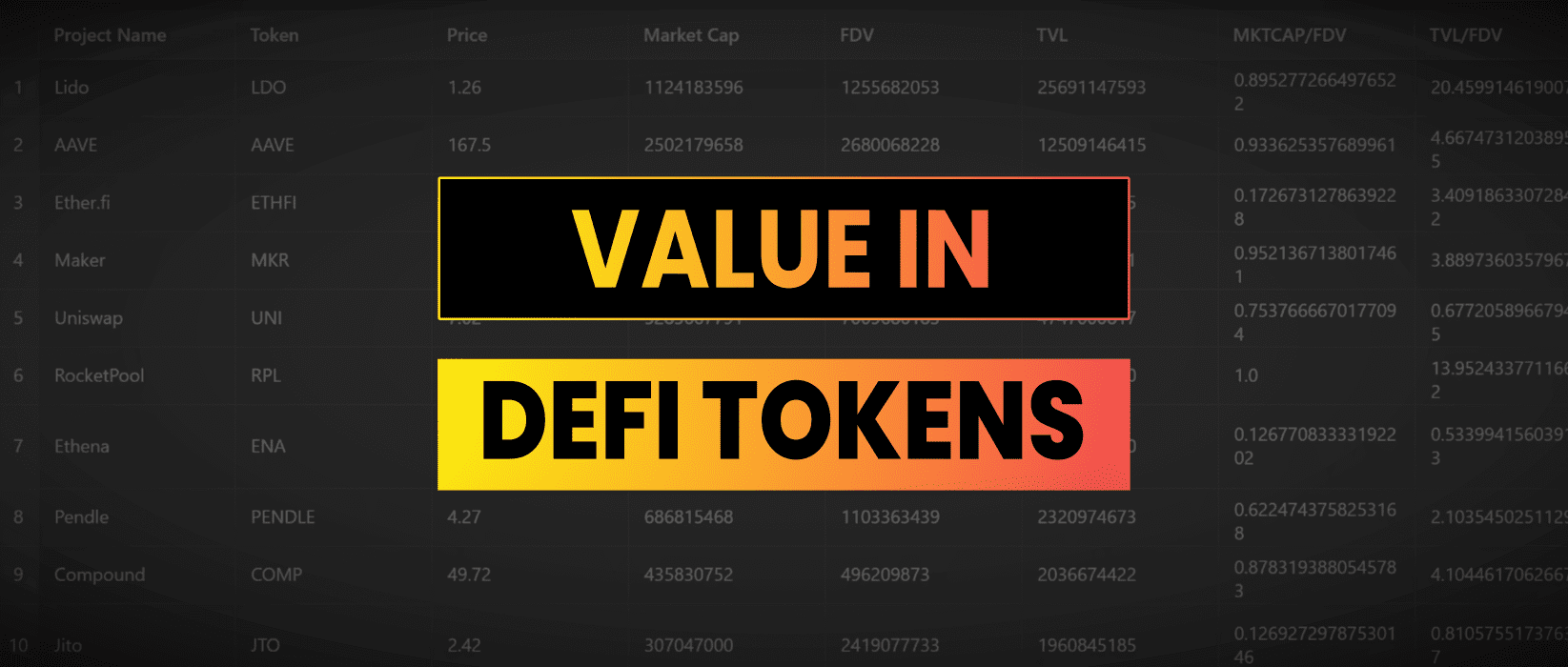
Value Investing In DeFi
For value investors the goal is to find assets priced below their intrinsic value, providing a margin of safety and potential for significant future growth. Could applying this principle to DeFi help identify underappreciated projects that are gaining significant traction. Let’s find out… Market Cap, TVL & FDV Market capitalization is the total value of
-

7 Problems That DeFi Solves
Last month Vitalik caused a stir when he suggested that DeFi “can’t be the thing that brings crypto to another 10-100x adoption burst” In this article I’m going to share my thoughts on why DeFi is still the no.1 most important use case for Ethereum. Lack of Financial Inclusion In a world where millions remain
-

3 Ways AI Will Change Software Development by 2030
As a developer who wrote his first computer program on a Commodore64, I’ve seen my fair share of technological shifts. But nothing quite compares to the seismic changes I anticipate large language models will bring to software development in the coming years. Let me take you on a journey through my vision of the future,
-

Building Rust Smart Contracts On Stellar Soroban
Soroban is the smart contract platform that allows developers to write and deploy smart contracts on the Stellar network. This tutorial will guide you through the process of building a simple smart contract using Rust and deploying it to Soroban. I recently took on the role of Developer in Residence with Stellar and this is
-

Pump.fun Clone In Solidity
Pump.fun is a token factory that lets users create and trade memecoins on Solana with dynamic pricing along a bonding curve. In this article I’ll show how I went about converting this concept to Solidity and deploying it on Ethereum. Full code for this is open source at: https://github.com/jamesbachini/Pump.sol Token Factory Contract At the core
-

Over-Collateralized Lending In DeFi
Decentralized finance has opened up many possibilities for holders of digital assets. One of the products which has gained traction over the last few years has been over-collateralized lending which is now a $30+ billion dollar industry. In this article I’m going to look at how over-collateralized lending works, why would someone want to do
-

Creating Your Own Oracle Solidity & NodeJS
In this tutorial I’m going to go through the steps to setting up your own oracle service to bring data on-chain. We are going to be deploying a simple smart contract, then setting up a NodeJS client to fetch the price of Bitcoin, then uploading this to the contract. Full code for this is open
-

Format JSON Tool
A simple tool to lint and format JSON because I was fed up of using the ones covered in ads. Format JSON The Javascript code that makes this work is quite simple: It can be used to format outputs prior to displaying the results of API queries or any other JSON found wild around the
-

Best Sketch To Image AI Generator
Recent developments in AI image generation have led to the availability of tools which can convert your doodles into generative images. Here is an example run across some freemium web apps: FreePik https://www.freepik.com/pikaso/sketch OpenArt https://openart.ai/create?mode=create NewArc https://www.newarc.ai/ ChatGPT https://chatgpt.com/ WindyBot https://windybot.com/editor Which Is The Best AI Sketch To Image Generator? As of September 2024 I
-

The Future Of Bitcoin, Ethereum & Web3
In this article I’m going to discuss where I think the industry is going over the next decade and how emerging developments will affect the following: Bitcoin Bitcoin, the pioneer and household name of crypto, has not evolved significantly from its origins as a digital currency. It is becoming increasingly recognized as a mainstream financial
-

What’s Happened Since Chip War
After reading Chip War by Chris Miller I was intrigued to see what developments have taken place since the book was written and if Moore’s Law is still alive and well. TSMC & Taiwan Strait Taiwan Semiconductor Manufacturing Company has maintained its position as the world’s leading chip manufacturer. The company announced ambitious plans for
-

What Are Blockchains Good For?
This article explores the strengths, limitations, and potential applications for blockchain technology. I will delve into six primary areas where blockchain technology shows promise: Transparency Blockchains are inherently transparent, making it a powerful tool for enhancing trust, accountability, and security in various applications. This transparency is evident in how transactions are recorded on a publicly
-

How To Calculate Gas Costs For Solidity Contracts
Deploying Solidity smart contracts can be expensive because the code needs to be stored on the shared storage of a decentralized peer to peer blockchain network. The dollar cost of deploying Solidity smart contracts is dependent on a number of variables: I’ve previously provided code to analyze the bytecode size of contracts, you can also
-

Are We Living In A Simulation?
In the vast expanse of human thought and philosophical inquiry, few questions are as mind bending and provocative as the simulation hypothesis. This idea, popularized by philosophers and futurists, posits that our reality the world we perceive, interact with, and call home might be nothing more than an incredibly advanced computer simulation. The Simulation Hypothesis
-

NFT Token Vault Solidity
This was inspired by the CryptoKitties WG0 token vault which accepts gen zero CryptoKitty deposits and mints 1 ERC20 token for each. Users can then buy tokens on exchange and claim NFT’s from the vault. The code is open source and available at: https://github.com/jamesbachini/NFTvault How The NFTvault Contract Works When you deposit your NFTs into
-

Creating an UpOnly ERC20 Token
In this tutorial we are going to create a ponzi game in the form of an ERC20 token that has an internal marketplace function. The idea is to increase the price over time so that early buyers get to dump on late buyers at a higher price. The last buyer will have no liquidity to
-

Solidity Encrypted Messaging dApp
This morning Pavel Durov, founder of Telegram, was arrested at a French airport for refusing to provide backdoor access to the messaging application. This tutorial will demonstrate how to use Elliptic Curve Diffie Hellman (ECDH) cryptography to establish a shared secret and encrypted messaging across a insecure communication channel, in this case a public blockchain.
-

CryptoKitties Investment Thesis
Below I have outlined the reasons why I invested my kids college fund into pictures of cats and why CryptoKitties are my highest conviction bet in the NFT space. Historical Significance CryptoKitties hold a unique place in the history of blockchain adoption and NFTs. It was the first time I remember the Ethereum network becoming
-

7 Incredible Use Cases For ChatGPT
ChatGPT has become an invaluable tool since it’s release in 2022. Here are seven amazing use cases which you can take advantage of today. Language Partner Learning a new language can be challenging, vraiment difficile, but ChatGPT can serve as an invaluable language partner. ChatGPT’s chat feature can be utilized as a voice tutor, it
-

Script To Analyze Bytecode Size Of Smart Contracts
I was having trouble with the hardhat bytecode plugin so I wrote a little nodejs script which will print off the size of my compiled Solidity contracts. You’ll need nodejs installed and can then run it like this. You should get an ouput like this: Here’s the code to save to analyze_bytecode.js file in the
-

Solidity Virtual Pet
Let’s create a virtual pet in Solidity and deploy it to the blockchain. Full frontend and contract code for this tutorial can be found here: https://github.com/jamesbachini/Solidity-Virtual-Pet Demo here: https://jamesbachini.com/misc/SolidityPet/index.html Smart Contract Our pet is going to have two attributes for hunger and happiness. Hunger should increase over time and happiness should have a mechanism where
-

How To Scrape Twitter/X Without API Access
Scraping Twitter/X without direct API access can be accomplished by leveraging third-party services like RapidAPI, which provides a streamlined way to interact with Twitter data. In this tutorial, we’ll walk through the process of using RapidAPI to scrape tweets from a specified user. I’m going to provide code snippets in Python and NodeJS for this